3.2.1 - Example
Identify Key Runtime Components
Examine the application’s behaviour at runtime by reviewing the Burp history or the network tab in your browser’s development console. This will help you determine if any extraneous calls are being made by the JavaScript frameworks, which could reveal functionality not displayed in the user interface.
Additionally, conduct a thorough walkthrough of the application to understand its operational flow. Observe how data is processed, stored, and reflected across various components of the application. This hands-on exploration is crucial to grasp the complete lifecycle of data within the system.
Furthermore, compile an inventory of all the functionalities the application incorporates, such as XML parsing, file uploads, SQL queries, and how it handles user-supplied input. Cataloging these functionalities will aid in identifying potential vulnerabilities. Each identified function should then be assessed for security risks and mapped in the requirements traceability matrix (RTM). This systematic evaluation ensures that all security aspects are addressed and aligned with the specific requirements of the project.
Browsing trough the app we find the following calls in our Burpsuite history, nothing we did not already expect to catch from our initial review.
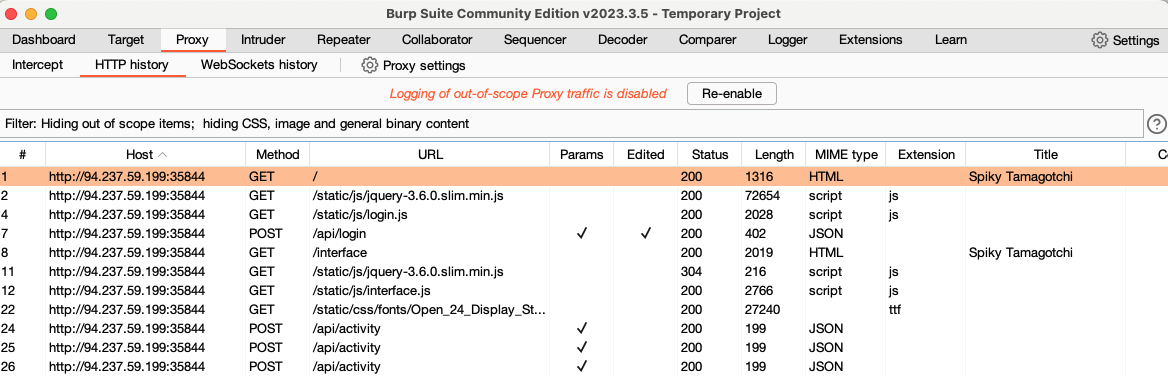
For now we will mostly focus our attention on these 2 functions. These are the calls that are associated with the potential SQLI and RCE from our RTM
screenshot-1
screenshot-2
| Feature ID | Description | potential Vulnerability | Test Method | References |
|---|---|---|---|---|
| F001 | User Authentication | JWT is prone to signature bypasses | SCA should point out CVE. There is also other methods of attack that need to be tested described here: https://portswigger.net/web-security/jwt |
|
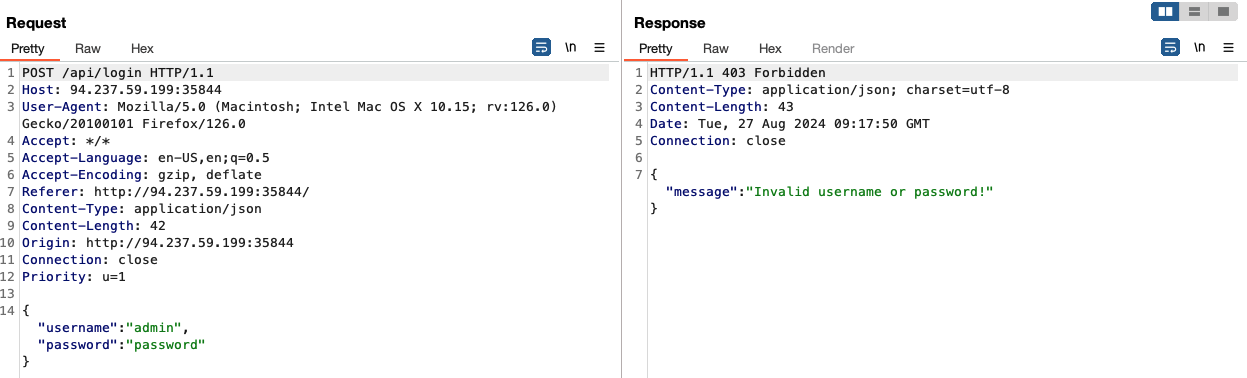
| F002 | User login | SQLI | A potential POC can be build following this resource. https://flattsecurity.medium.com/finding-an-unseen-sql-injection-by-bypassing-escape-functions-in-mysqljs-mysql-90b27f6542b4 |
Screenshot-1 |
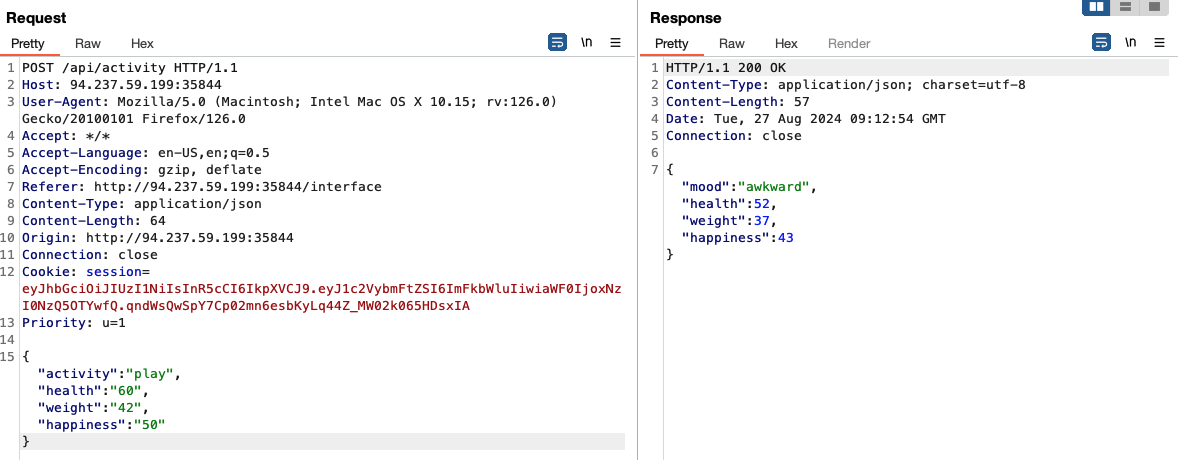
| F003 | SpikyFactor.js | RCE | SonarQube detected a potential RCE in the calculate function of the challenge/helpers/SpikyFactor.js |
Screenshot-2 |