2.1.1 - Example
List All Application Components
From the Dockerfile we can learn that in this scenario it is a fairly straightforward nodeJS application with a mysql database
FROM node:alpine
# Install packages
RUN echo 'http://dl-cdn.alpinelinux.org/alpine/v3.6/main' >> /etc/apk/repositories
RUN echo 'http://dl-cdn.alpinelinux.org/alpine/v3.6/community' >> /etc/apk/repositories
RUN apk add --update --no-cache supervisor mariadb mariadb-client curl
# Setup app
RUN mkdir -p /app
# Add application
WORKDIR /app
COPY challenge .
# Install dependencies
RUN yarn
# Setup superivsord
COPY config/supervisord.conf /etc/supervisord.conf
# Expose the port node-js is reachable on
EXPOSE 1337
# Populate database and start supervisord
COPY --chown=root entrypoint.sh /entrypoint.sh
ENTRYPOINT ["/entrypoint.sh"]
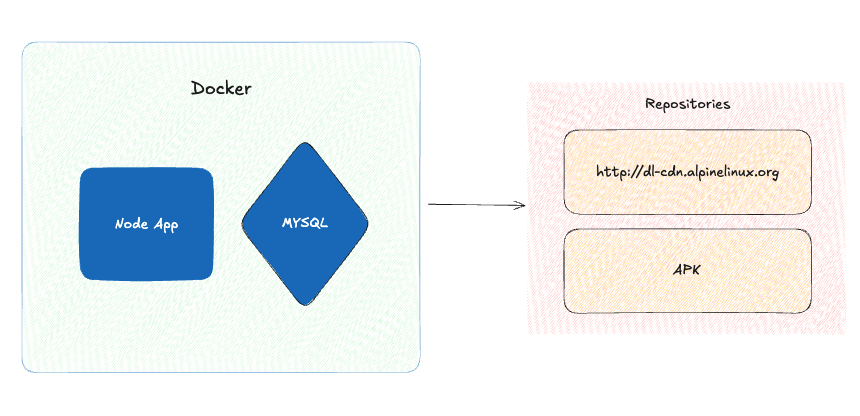
Visualize Data Flow
This is just simply clicking trough the application and get a good idea how it behaves and where data is being reflected etc. Examples could be:
- whenever we fill in a form does the output get reflected into a Administration panel that we can initially not see with our low level user.
- Does data that we input get used in iie a file name?
- Does data that we input get used in an XML form?
- Does data that we input get send to 3rd party applications? So, how does the application behave and how does user supplied input move trough the application
Map External Interactions and Dependencies
In this example we will find that the application downloads packages from the CDN of http://dl-cfn.alpinelinux.org and apk. Since they don’t use their own registry it might me interesting to verify type-squatting level mistakes in the package files to verify if we can distribute malware via supply chain attacks.
Identify Security Controls
We found that authentication/authorization decisions are being made by means of JWT
-> "jsonwebtoken": "^8.5.1",
->/web_spiky_tamagotchi/challenge/middleware/AuthMiddleware.js
For now let’s make note of this finding in our RTM so we can investigate it later.
| Feature ID | Description | potential Vulnerability | Test Method |
|---|---|---|---|
| F001 | User Authentication | JWT is prone to signature bypasses | SCA should point out CVE. There is also other methods of attack that need to be tested described here: https://portswigger.net/web-security/jwt |